Understanding Site to Site VPNs: Understanding Site to Site VPNs, IPsec VPNs, and Enterprise VPN Solutions
Understanding site to site vpns
Understanding site to site vpns is all about securely connecting multiple networks over the internet so they appear as one seamless network. This guide breaks down what they are, how they work, real-world use cases, and how to choose the right setup for your business. Think of it as a practical, friend-to-friend walkthrough that helps you make informed decisions without the jargon.
Quick facts to set the stage
- A site-to-site VPN securely links two or more networks, typically at different physical locations, over the public internet.
- There are two common types: 1 intranet-based site-to-site VPNs for private networks and 2 extranet-based site-to-site VPNs for partner networks.
- IPsec is the most widely used protocol suite for site-to-site VPNs, handling encryption, authentication, and data integrity.
- Site-to-site VPNs can be gateway-to-gateway, where each network has a VPN gateway router or firewall that handles the secure tunnel.
In this guide you’ll find:
- What a site-to-site VPN is and when to use it
- How IPsec works in site-to-site deployments
- Key components and common topologies
- Setup steps for a typical gateway-to-gateway VPN
- Security, performance, and reliability considerations
- Real-world use cases and ROI
- A practical checklist before you deploy
- FAQ with practical answers
What is a site-to-site VPN, and when should you use one?
- Core idea: Instead of letting users connect individually to a single remote network client-to-site VPN, a site-to-site VPN creates a secure tunnel between two or more networks so devices on either side communicate as if they’re on the same LAN.
- When to use:
- Multiple branch offices need secure, constant connectivity for internal apps, directory services, file shares, and backups.
- Partners or suppliers require access to your network without giving them direct, individual user credentials.
- You want centralized policy control at the router/firewall level rather than configuring each endpoint.
- Benefits:
- Centralized security management and simpler user access control
- Reduced management overhead for remote sites
- Improved performance for site-wide network traffic that doesn’t require individual VPN clients
How IPsec powers site-to-site VPNs
- IPsec Internet Protocol Security provides three core functions:
- Authentication: Verifies that the traffic comes from a trusted peer
- Encryption: Keeps data confidential in transit
- Data integrity: Ensures data isn’t tampered with during transit
- Typical IPsec workflow:
- IKE Internet Key Exchange negotiates the security associations SAs and cryptographic keys
- ESP Encapsulating Security Payload encrypts and authenticates the actual data
- AH Authentication Header may be used in some cases, but ESP is more common for site-to-site
- Modes:
- Transport mode is mostly for end-to-end host communication, not common for gateway-to-gateway.
- Tunnel mode is the standard for site-to-site, wrapping the whole IP packet inside an IPsec packet.
Key components and topologies
- VPN gateways: Routers or firewalls at each site that terminate the IPsec tunnel. They handle encryption, decryption, and policy enforcement.
- Tunnel endpoints: The specific interfaces or IP addresses where the IPsec tunnel is established.
- Policies and proposals: The cryptographic algorithms, key lifetimes, and other negotiation settings used to form SAs.
- Common topologies:
- Hub-and-spoke: A central site connects to multiple branch offices through a single hub site. Traffic between spokes routes via the hub unless a full-mesh is configured.
- Full mesh: Every site connects directly to every other site. This can be more scalable for many sites but more complex to manage.
- Point-to-point two sites: Simple, ideal for a single branch office pair.
Typical setup steps for a gateway-to-gateway VPN
- Step 1: Define requirements
- Identify the exact sites to connect, expected traffic patterns, and whether you’ll route only specific subnets or all traffic between sites.
- Step 2: Choose devices and compatibility
- Ensure both sites’ gateways support IPsec, IKE versions, and the same crypto algorithms or that you can negotiate a compatible set.
- Step 3: Plan addressing and subnets
- Use non-overlapping private subnets. Document LAN networks and the subnets you’ll allow through the VPN.
- Step 4: Configure IPsec policies
- Select phase 1 IKE settings: encryption algorithm, hashing, authentication method, and PFS perfect forward secrecy.
- Select phase 2 IPsec settings: encryption, integrity, and lifetime.
- Step 5: Establish tunnel endpoints and routing
- Define the tunnel endpoints’ public IPs, configure the tunnel mode, and set up static routes or dynamic routing to steer traffic through the VPN.
- Step 6: NAT considerations
- If devices behind the gateways use NAT, configure NAT-T NAT Traversal so IPsec can traverse NAT devices.
- Step 7: Authentication and access control
- Use pre-shared keys PSK or digital certificates. Implement access control lists ACLs or firewall rules to permit only desired subnets.
- Step 8: Testing and validation
- Verify SA establishment, monitor lifetimes, test failover, and confirm that traffic routes correctly between sites.
- Step 9: Monitoring and maintenance
- Set up logging, alerting for tunnel bring-up/down events, and periodic reviews of crypto settings to stay current with security best practices.
Security, performance, and reliability considerations
- Encryption and algorithms:
- Prefer modern algorithms AES-256 for encryption, SHA-256/2 for integrity. Avoid deprecated suites.
- Key management:
- Use certificates where possible for easier rotation and revocation; if you use PSKs, rotate them regularly.
- Perfect Forward Secrecy PFS:
- Enable PFS to ensure that a compromise of one key does not affect past session data.
- Redundancy:
- Consider multiple tunnels or secondary gateways for failover. An active-passive setup can minimize downtime.
- QoS and traffic shaping:
- Reserve bandwidth for critical inter-site traffic, especially for voice, video, or large file transfers.
- NAT traversal:
- Ensure NAT-T is enabled if either gateway sits behind a NAT device; otherwise, tunnels may fail to establish.
- Reducing latency and jitter:
- Optimize routing and, when possible, avoid unnecessary hub-and-spoke traffic where direct site-to-site routes are preferable.
- Security best practices:
- Regularly update firmware on gateways, monitor for CVEs related to your devices, and implement least-privilege firewall rules.
Real-world use cases and ROI
- Branch office enablement:
- A retail company with multiple stores uses a site-to-site VPN to connect each store to the main data center for inventory, POS systems, and centralized analytics.
- Partner networks:
- A manufacturing firm links its ERP system to a supplier’s network, enabling secure data exchange without exposing individual users.
- Data center extension:
- A cloud-first company extends its on-prem resources to a regional data center, enabling consistent access to shared services and backups.
- ROI considerations:
- Reduced WAN costs compared to MPLS for certain traffic
- Faster deployment of new sites compared to dedicated circuits
- Centralized security policies reducing management overhead
Checkpoint: a practical deployment checklist
- Confirm all sites’ network subnets are non-overlapping
- Verify hardware compatibility and firmware versions across gateways
- Decide between hub-and-spoke vs full mesh based on site count and traffic patterns
- Plan IP addressing, routing, and whether to use dynamic routing
- Choose authentication method PSK vs certificates
- Enable NAT-T if needed and test with realistic traffic
- Implement robust logging and monitoring
- Schedule regular crypto and policy reviews
- Prepare a rollback plan in case of tunnel failures
Common mistakes to avoid
- Overlapping subnets that break routing
- Weak encryption or outdated algorithms
- Inadequate monitoring leading to undetected tunnel drops
- Complex, hard-to-maintain hub-and-spoke topologies without automation
- Failing to test failover and disaster recovery scenarios
Security tips and best practices
- Regularly rotate keys or certificates
- Use strongest practical encryption and keep devices updated
- Segment tunnels with granular firewall rules
- Prefer certificate-based authentication for scalable management
- Document all tunnel configurations and changes for auditing
Comparing popular site-to-site VPN solutions
- On-prem gateways Fortinet, Cisco, Juniper, Sophos, Palo Alto
- Pros: Mature ecosystems, advanced security features, strong performance
- Cons: Hardware cost, maintenance complexity
- Cloud-based VPN gateways Azure VPN Gateway, AWS VPN, Google Cloud VPN
- Pros: Seamless cloud integration, global scalability
- Cons: May require additional networking work for hybrid setups
- Open-source options strongSwan, OpenVPN in tunnel mode
- Pros: Flexible, cost-effective
- Cons: Requires expertise to deploy securely and maintain
Performance considerations by scenario
- Small office to data center:
- Favor AES-256, 2048+ bit DH groups, 1:1 traffic routing, QoS for critical apps
- Multi-branch network with heavy file transfers:
- Consider full mesh with optimized routing, multiple tunnels for redundancy
- Latency-sensitive workloads:
- Use direct site-to-site paths and minimize cross-hub traffic, tune MTU/MSS to reduce fragmentation
Vendor-neutral best practices
- Standardize on a single IPsec profile across sites when possible to reduce complexity
- Use centralized change management for VPN policy updates
- Maintain inventory of all VPN devices and keep firmware current
- Regularly test failover and backup tunnel scenarios
Storage and backups through VPNs
- If backups traverse VPN tunnels, ensure encryption in transit and consider dedicated backup windows to minimize performance impact
- Schedule recurring verification of restore capabilities to ensure data integrity across sites
Useful reading and advanced topics
- IPsec architecture and cryptography basics
- Firewall policy design for VPNs
- VPN monitoring and alerting best practices
- Secure remote access vs site-to-site VPNs: when to use each
FAQ section
Frequently Asked Questions
What is a site-to-site VPN?
A site-to-site VPN creates a secure tunnel between two or more networks over the internet so devices on either side can communicate as if they are on the same local network.
How does IPsec work in site-to-site VPNs?
IPsec authenticates peers, encrypts data, and ensures integrity. It negotiates cryptographic keys via IKE, then uses ESP to secure the actual traffic between gateways.
What are common topologies for site-to-site VPNs?
Hub-and-spoke, full mesh, and point-to-point are common topologies. Hub-and-spoke is great for many sites with a central hub; full mesh offers direct site connections.
What’s the difference between a site-to-site VPN and a remote access VPN?
Site-to-site connects networks at sites or offices; remote access client-to-site connects individual devices to a network. The former is gateway-to-gateway, the latter is user-to-network.
Do I need a dedicated device at each site for IPsec?
Usually yes. VPN gateways routers or firewalls at each site terminate the tunnel and enforce policies. The NordVPN Promotion You Cant Miss Get 73 Off 3 Months Free and More Great VPN Deals
Should I use PSK or certificates for authentication?
Certificates are generally more scalable and secure for many sites. PSKs are simpler but harder to manage at scale.
How can I ensure high availability for site-to-site VPNs?
Use redundant gateways, multiple tunnels, and automatic failover. Consider load balancing and health-check mechanisms.
How do I troubleshoot a VPN that won’t form?
Check gateway reachability, IPsec phase 1/2 negotiations, NAT-T settings if NAT is involved, firewall rules, and ensure subnets don’t overlap.
Can I route only specific traffic through the VPN?
Yes. You can create policies to route only certain subnets through the VPN while keeping other traffic to go directly to the internet.
What performance factors affect site-to-site VPNs?
Encryption overhead, tunnel MTU, routing efficiency, link latency, and the performance of VPN gateways. QoS can help prioritize critical traffic. Why Your VPN Might Be Blocking LinkedIn and How to Fix It
Useful URLs and Resources
- Understanding site to site vpns - Apple Website - apple.com
- IPsec basics - en.wikipedia.org/wiki/IPsec
- VPN topology best practices - en.wikipedia.org/wiki/Virtual_private_network
- Open-source VPN strongSwan - www.strongswan.org
- Cloud VPN services comparison - aws.amazon.com, azure.microsoft.com, cloud.google.com
- Network security best practices - nIST.gov
- VPN performance tuning - www.cisco.com
- Enterprise VPN design patterns - www.paloaltonetworks.com
- VPN monitoring and logging - www.solarwinds.com
- Firewall and VPN integration - www.fortinet.com
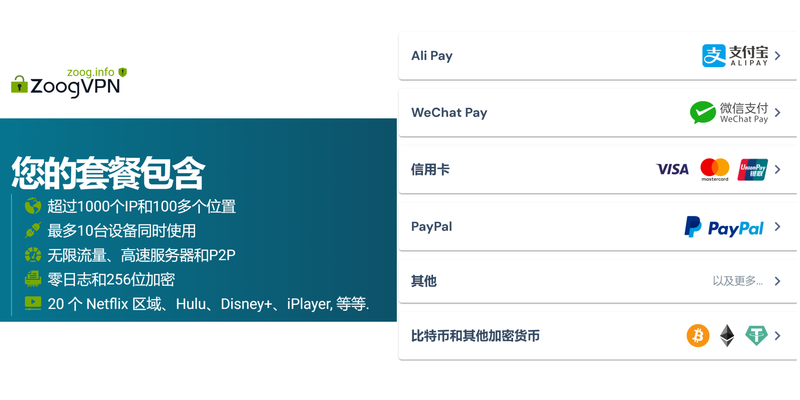
Promotional note If you’re considering a quick, secure, and reliable option for site-to-site VPNs, you might want to check out NordVPN for business needs. It’s known for robust security features and enterprise-grade options. Learn more at your convenience through the link provided: NordVPN
Sources:
How Many Devices Can I Use With Surfshark VPN An Unlimited Connection Guide For Your Digital Life
Clash verge rev:VPN 案例解析与实用指南,全面覆盖越界突破与隐私保护
Total vpn on linux your guide to manual setup and best practices Telus tv not working with vpn heres your fix
Which country vpn is fast in india
Softether vpn 클라이언트 완벽 가이드 무료 vpn 설정부터 활용법까지 2026년 최신: 속도, 보안, 무료 설정 팁까지 한눈에 보는 실전 가이드